Wireless Hacking
Wireless networks broadcast their packets using radio frequency or optical wavelengths. A modern laptop computer can listen in. Worse, an attacker can manufacture new packets on the fly and persuade wireless stations to accept his packets as legitimate.The step by step procerdure in wireless hacking can be explained with help of different topics as follows:-
Stations and Access Points A wireless network interface card (adapter) is a device, called a station, providing the network physical layer over a radio link to another station.
An access point (AP) is a station that provides frame distribution service to stations associated with it.
The AP itself is typically connected by wire to a LAN. Each AP has a 0 to 32 byte long Service Set Identifier (SSID) that is also commonly called a network name. The SSID is used to segment the airwaves for usage.
Wired Equivalent Privacy (WEP) It is a shared-secret key encryption system used to encrypt packets transmitted between a station and an AP. Wired Equivalent Privacy (WEP) is a security protocol, specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11b, that is designed to provide a wireless local area network (WLAN) with a level of security and privacy comparable to what is usually expected of a wired LAN.
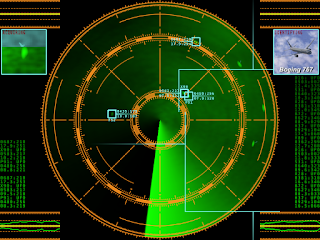
Wireless Network Sniffing :- Sniffing is eavesdropping on the network. A (packet) sniffer is a program that intercepts and decodes network traffic broadcast through a medium. It is easier to sniff wireless networks than wired ones. Sniffing can also help find the easy kill as in scanning for open access points that allow anyone to connect, or capturing the passwords used in a connection session that does not even use WEP, or in telnet, rlogin and ftp connections.
Passive Scanning :- Scanning is the act of sniffing by tuning to various radio channels of the devices. A passive network scanner instructs the wireless card to listen to each channel for a few messages. This does not reveal the presence of the scanner. An attacker can passively scan without transmitting at all.
Detection of SSID :- The attacker can discover the SSID of a network usually by passive scanning because the SSID occurs in the following frame types: Beacon, Probe Requests, Probe Responses, Association Requests, and Reassociation Requests. Recall that management frames are always in the clear, even when WEP is enabled.
When the above methods fail, SSID discovery is done by active scanning
Collecting the MAC Addresses The attackers collect legitimate MAC addresses of victim for use later in constructing spoofed frames. The source and destination MAC addresses are always in the clear in all the frames.
Collecting the Frames for Cracking WEP The goal of an attacker is to discover the WEP shared-secret key. The attacker sniffs a large number of frames An example of a WEP cracking tool is AirSnort ( http://airsnort.shmoo.com ).
Wireless Spoofing There are well-known attack techniques known as spoofing in both wired and wireless networks. The attacker constructs frames by filling selected fields that contain addresses or identifiers with legitimate looking but non-existent values, or with values that belong to others. The attacker would have collected these legitimate values through sniffing.
MAC Address Spoofing The attacker generally desires to be hidden. But the probing activity injects frames that are observable by system administrators. The attacker fills the Sender MAC Address field of the injected frames with a spoofed value so that his equipment is not identified.
IP spoofing Replacing the true IP address of the sender with a different address is known as IP spoofing. This is a necessary operation in many attacks.in other we can say that it just like ip masking
Frame Spoofing The attacker will inject frames that are valid but whose content is carefully spoofed.
Wireless Network Probing The attacker then sends artificially constructed packets to a target that trigger useful responses. This activity is known as probing or active scanning.
Trojan AP An attacker sets up an AP so that the targeted station receives a stronger signal from it than what it receives from a legitimate AP.
Denial of Service A denial of service (DoS) occurs when a system is not providing services to authorized clients because of resource exhaustion by unauthorized clients. In wireless networks, DoS attacks are difficult to prevent, difficult to stop. An on-going attack and the victim and its clients may not even detect the attacks. The duration of such DoS may range from milliseconds to hours. A DoS attack against an individual station enables session hijacking.
War Driving The act of driving around in a vehicle with a laptop computer, an antenna, and an 802.11 wireless LAN adapter to exploit existing wireless networks.
Regardless of the protocols, wireless networks will remain potentially insecure because an attacker can listen in without gaining physical access.










Here Is A Colletion Of Huge Programs, Download Free Software, Books,Project Etc.
ReplyDeleteYou Also Can Learn C, C++, Java ,ASP.Net And Blog & Website Designing
http://www.programmingwithbasics.com